|
 |
Learning to use tools which can actually aid in overcoming the adversary is difficult. To begin with, there’s the difficulty of knowing what the adversary is going to do, why they’re going to do it, and the signs that they’re actually doing it now. Not an easy task whatsoever. However, there is also the matter of understanding what we can do, how we can do it, and when it is appropriate to do it—because, when we know that, we can start to get a step ahead.
And, of course, this kind of knowledge doesn’t come easily and is often hard-won. In fact, it is often hard-won and then quickly becomes out of date as the threat landscape changes. Because of that, understanding practical approaches to cybersecurity and being able to flex your practical chops when the pressure is on is at the heart of becoming a successful practitioner today.
And who better to ask about this than someone sitting on the frontlines?
Hack Before You Launch is a practical, live workshop designed for developers, indie hackers and fast-moving builders who are using AI tools like ChatGPT and Copilot or simply plugging in and vibe coding to build and ship products faster than ever. While AI can accelerate development, it can also introduce hidden security vulnerabilities that often go unnoticed until it’s too late. In this session, ethical hacker Dr. Katie Paxton-Fear will demonstrate exactly how AI-generated applications can be exploited in the real world—and, more importantly, how to fix those issues before attackers find them first.
This is not a theoretical webinar. Attendees will watch a real AI-built application being tested for authentication flaws, prompt injection risks, and insecure data handling. Katie will walk through how attackers think, how vulnerabilities are uncovered, and the practical steps developers can take to protect their apps before launch. By the end of the session, participants will leave with a clear pre-launch security checklist and a better understanding of whether their product is truly ready to ship.
What you need to know
Learn how AI-generated applications can introduce hidden security vulnerabilities
Watch a live demonstration of real-world exploits, including authentication flaws and prompt injection
Understand how attackers identify and exploit weaknesses in applications
Discover practical, lightweight methods for identifying and fixing security issues
Leave with a simple pre-launch security checklist to use before deploying your app
Ideal for developers, indie hackers, startup founders, and anyone building with AI-assisted code tools
Important event information
Date: Saturday, 30 May
Time: 10:00 AM – 11:30 AM
Duration: 1 hour 30 minutes
Speaker: Dr. Katie Paxton-Fear
And while we’re waiting for that, maybe it’s time to think about a particular tool which could come in handy—perhaps something that we looked at in brief last week.
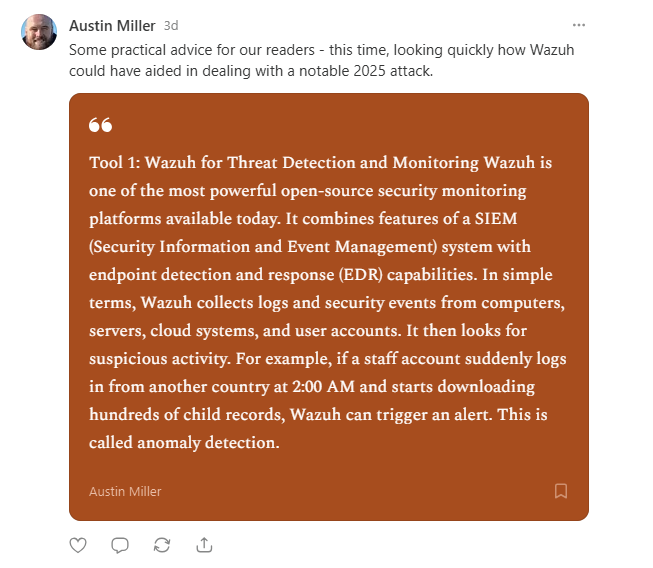
How Using Wazuh Gets You Ahead
1. Install Wazuh Agents Across Endpoints
The first step in using Wazuh is deploying Wazuh agents on all important endpoints, including staff laptops, servers, domain controllers, cloud systems, and databases. These lightweight agents continuously collect security logs and monitor system activity such as logins, file access, software installations, and system changes.